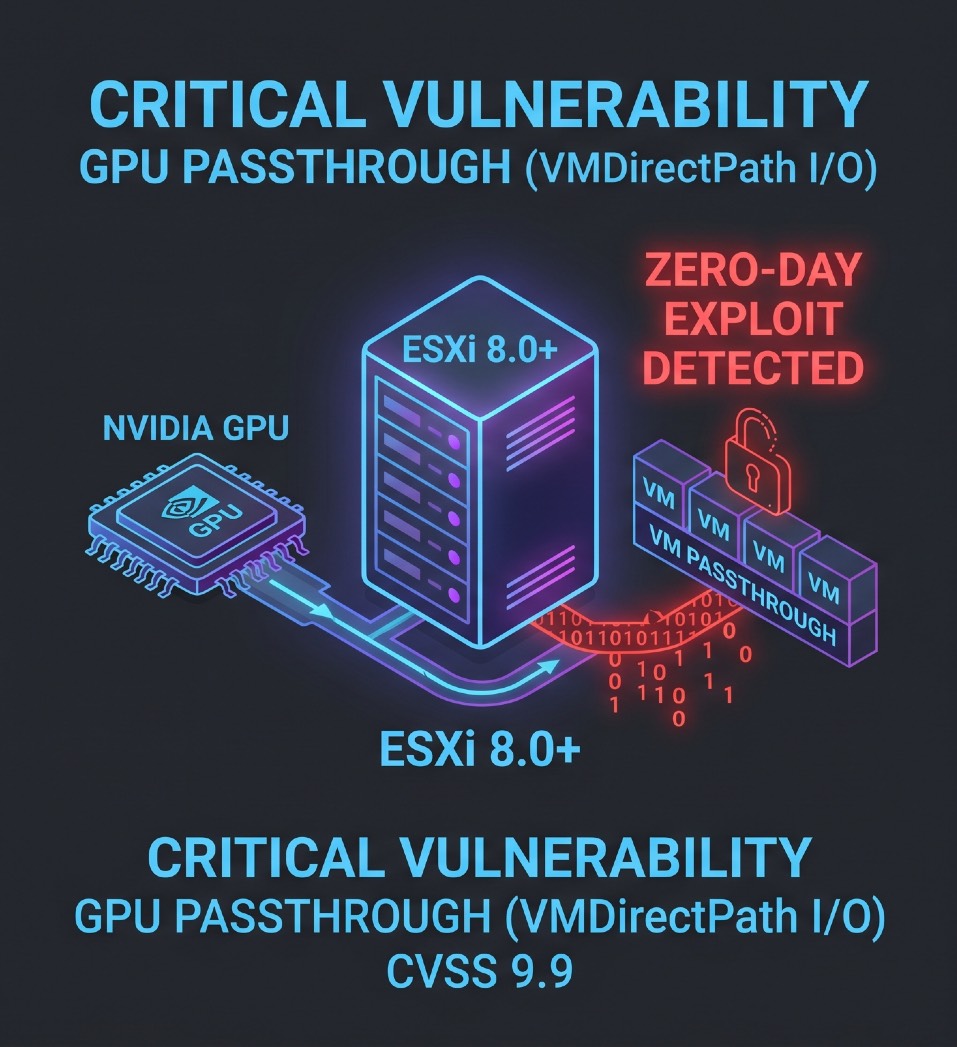
ZERO-DAY: ESXi 8 GPU PASSTHROUGH VULNERABILITY EXPLOITED IN THE WILD
**Threat Actor:** Advanced Ransomware Syndicates (RansomHub)
**Target:** VMware ESXi 8.0+ Infrastructure (Specifically GPU/PCIe Passthrough Nodes)
**The Intelligence:**
A severe, unpatched Zero-Day vulnerability (CVSS 9.9) is currently being exploited in the wild targeting VMware ESXi version 8 environments. Threat intelligence indicates attackers are specifically hunting hypervisors configured with hardware passthrough (VMDirectPath I/O)—particularly those utilizing NVIDIA GPUs for AI, rendering, or heavy compute workloads.
**Key Incident Details:**
• The Exploit: The vulnerability exists within the memory management of the PCIe passthrough layer. Attackers who gain initial access to a guest VM can execute a "Hypervisor Escape," breaking out of the virtual machine to execute code directly on the underlying ESXi host root shell.
• The Payload: Once host access is achieved, the threat actors are deploying a compiled Linux ransomware encryptor, instantly locking all datastores (.vmdk, .vmx files) and shutting down the entire virtualized cluster.
• The Impact: Several high-profile data centers and AI-research labs have already reported total infrastructure lockouts over the past 48 hours.
**Strategic Assessment:**
This is a catastrophic vulnerability for modern data centers and advanced labs running ESXi 8 with hardware acceleration. Administrators utilizing GPU passthrough (especially with NVIDIA RTX or Enterprise cards) should immediately audit guest VM access, restrict host SSH/management interfaces, and monitor network traffic for anomalous outbound connections until an emergency patch is released by Broadcom.